Introduction
Compromised credentials can quickly snowball into complex kill chains that can cripple entire networks and the speed of compromise has only gotten faster over time, leaving defensive teams scrambling to keep up. Password policies can be a crucial defense-in-depth component to mitigate credential compromise. But even with organizations that enforce complexity and 12 character + passwords, we still frequently uncover weak passwords on both internal and external networks during penetration tests.
The root issue is technically a weak password policy, but usually it’s that the password policy is not sufficiently filtering weak passwords, also known as deny-listing, black-listing, or block-listing. There are numerous security policies, frameworks, and standards that can inform how an organization should implement their password policies and sometimes regulatory compliance like PCI can also affect implementation. We have seen most organizations move towards enforcing complexity, password length, and removing frequent password rotations. Thankfully NIST has recently recommended removing mandatory password expiration as, more often than not, any frequent password expiration policy usually encourages poor password selection.
Despite all of this, we still frequently compromise weak passwords due to poor filtering. There does not appear to be a lot of clear documentation that describes accurately what this problem is beyond surface level guidance on avoiding seasonal passwords like “Summer2025!” or company-based passwords like “Company123.” With this blog, I’m hoping to provide a resource to describe what this issue actually is, document some examples of frequent patterns and schemes we’ve seen that lead to compromising weak passwords, and provide some observations and recommendations to help organizations better approach their password policies.
The Problem
Authentication is one of the foundational concepts of information security that, to the misfortune of defensive security practitioners, usually relies on every employee of the organization to properly implement. Users and employees must verify their identity somehow in order to gain access to corporate resources and historically that has been handled by passwords, usually dictated by a password policy. While there are additional methods of authentication besides passwords, by default most systems and organizations require them and it represents a significant attack surface for threat actors to target. Additionally, authentication is usually a problem of scale: the more employees and end users in an organization, the larger the chance that at least one account has a weak password due to the human element of password selection. While password policies have improved over the last few years and most organizations now recognize the danger of frequent password rotations (We’re all looking at you PCI), the frequent defense of “strong” password policies is still mostly rooted in length and complexity requirements.

The unfortunate truth is that it is very rare for length and complexity to change whether we compromise passwords or not during our engagements since the human element is often very predictable. Capitalization of the first letter, ending a combination of numbers and special characters, and sufficiently long base words in the middle is usually a reasonable assumption for any password not generated by a password manager. An understated complication regarding password policies is the unfortunate side effect that even if a policy is updated which forces users to choose “stronger” passwords, weak passwords will linger as variations of historical passwords. In what I like to call a “credential straying” attack, a combination of credential spraying and stuffing, users are likely to modify their passwords just enough to satisfy the password policy requirements from previously selected passwords. This can be made worse if organizations provide(d) standardized onboarding or password reset schemes. I will go into more detail in the following section of common patterns of weak passwords, but tackling password policies beyond mere compliance theatre is no easy feat since the sins of older policies will often be visited upon later policy updates.
Before getting into specific examples, I also wanted to discuss what I mean by “weak” passwords. There are two main contexts that I use to inform discussions of weak passwords: weak passwords as in “guessable” and weak passwords as in “crackable”. Guessable passwords can be compromised in password spraying or brute force attacks involving relatively few attempts. Crackable passwords refers to the process of obtaining a plaintext password from an intercepted or compromised password hash with offline resources. This is dedicated password cracking hardware capable of many millions+ attempts per second, typically involving wordlists and rules or defined patterns called “masks.” For the purpose of this blog I will focus on “guessable” passwords since password policies have a better chance of addressing them. Plus, if an attacker is cracking your password hashes, you have bigger problems. If a password can be guessed easily, then the password policy’s filtering could likely be improved to prevent the selection of the weak password.
What I Talk About When I Talk About Password Filtering
So, let’s talk password filtering. The basics seem obvious, restrict seasonal and company related passwords like “Winter2025!” and “Company1!.” In most environments however with default filtering, it is still fairly trivial to guess passwords. It’s also problematic that most filtering solutions are very brittle and fail to address common edge cases. Take the classic password of “Summer2025!” for example. If a user attempts to use that password and is restricted, it is likely they will attempt variations of it that are easy enough to remember but still satisfy the password policy.

All of the above variations of summer are passwords I have seen numerous times during engagements. Add the usual capitalization, year number, and ending special character and it is not difficult to guess weak passwords that are 18 characters or longer. This problem can also extend to the special characters themselves. Microsoft’s Entra ID’s (current) password protection rules might not like passwords that end in “2025!” but will accept passwords that end in “25!!.” With a thousand valid usernames I can usually guess one in less than a day or two, attempting one per hour across the user list.
The type of base words that organizations should consider restricting when implementing password filtering is also typically much larger than standard default lists based around seasons, sports teams, and passwords with the word “password” in them. The address and building number where the company is located, the local towns where the employees likely live, even common passphrases such as “Ilovemykids” are common targets when attempting targeted password spraying (“guessing”) attacks. In addition to the company name itself, usually the type of business can inform base word selection when it comes to compromising passwords. Healthcare institutions should consider base words like “nursing” and department names, finance institutions should consider common banking and investment terms, and so on. These kinds of attacks have become even easier with the advent of AI/LLM since producing targeted password guesses tailored to the company is now easier than ever. Publicly available websites, Wikipedia pages, the geographic region of the business, and general inferences can be prompted by these models to produce suggestions of passwords to attempt.
Another common problem I see is predictable onboarding and/or reset password schemes. Even when the scheme might no longer be used, current variations of it likely exist. Once you give a user a password scheme it increases the likelihood that they will just continue to use variations of the given password. This can be general schemes like “YourFirstDay!” and “Welcome2Company!” or customized but predictable patterns usually based on employee names and id numbers. Once one similar password of this type is compromised, whether from a straight password guessing attack or from breach data, then these words and phrases can quickly lead to an increased risk of credential compromise that requires employee education and updated password filtering to address.
Some Recommendations
Unfortunately (which is a word I found myself unfortunately using too much in this blog), there is not an easy solution when it comes to proper password filtering that I am aware of. The process can quickly become a professional game of “whack-a-mole” as users take the path of least resistance by selecting passwords that will satisfy password policy requirements but are often predictable variations of common historically weak passwords. Due to scaling complexity, the calculus on how much effort large organizations should spend on password filtering can be vastly different than small to medium sized businesses. I might be biased, but organizations like Depth Security who specialize in compromising weak passwords can provide targeted insight to help organizations calculate the actual strength of their password policy to help navigate these questions.
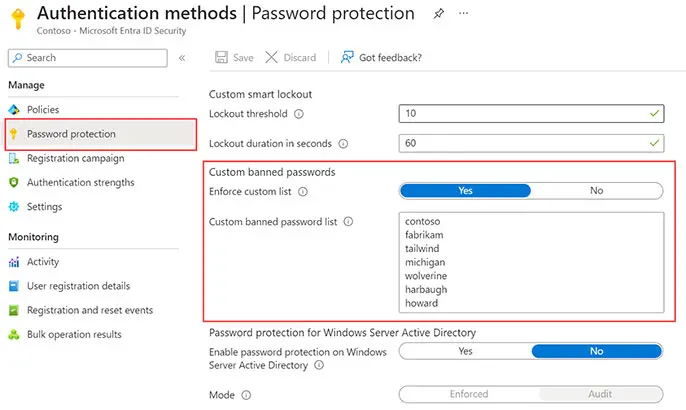
There are direct Microsoft solutions to protect Active Directory environments such as Entra ID password protection as well as third-party solutions that can help restrict weak passwords but typically any solution is not going to be a one size fits all and companies will have to spend time and resources to ensure that specific business context is being accounted for. Additionally, once a password filter list is implemented or supplemented it must be continually updated and evaluated for it to remain effective.
A shortcut I like to suggest to any company looking to bolster their password policy is to conduct a targeted password audit to uncover weak passwords and weak password schemes to help inform any password filtering solution and password rotation enforcement. It’s often easier to work backwards by analyzing Active Directory passwords hashes than it is to conduct a point-in-time network test which may not accurately represent the actual risk a real-world attacker with more time and resources might spend on password spraying attacks. The same AI prompts that I mentioned earlier than can help attackers make targeted password attacks can also be used by defenders to help inform custom lists for password filtering solutions as well.
If your company is unaware of how to conduct a password audit inhouse feel free to contact me with any questions and I would be happy to point you in the right direction. However, I do feel that there is an art to compromising passwords, whether through guessing or password cracking, and insight can be gained from utilizing a company like Depth Security who has the experience and knowledge on how to perform a targeted password audit that uses experience and intuition. Again, excuse the bias, but recognizing password schemes, company specific password choices, and guessable patterns is easier to accomplish with a trusted partner but at the end of the day any password audit is better than no auditing whatsoever.
To address the human side of the problem, encouraging (or mandating if you have enough business capital) the use of password managers can prevent the selection of weak passwords altogether. Also consider supplementing any implementation of a password policy with employee training on password selection. If password managers are not used, encourage the use of long passphrases with variations on any added complexity. Encourage deliberate misspellings, added characters in random points, and modifications/complexity of common passphrases to take place in the middle of the passphrase versus the start or end. Organizations can also consider implementing passwordless authentication that typically requires the employee to prove authentication with something they have versus something they know to avoid weak passwords altogether.
Conclusion
I do not envy any organization that has to enforce password policies, and I certainly recognize that business considerations such as impeding workflows, user adoption, and help desk friction can all be factors that influence how password policies are handled. Any organization seeking to properly address weak password policies by implementing strong password filtering has an uphill battle since it deals with human nature when it comes to password selection. I hope this blog helps describe what can make a password policy still weak despite meeting the complexity, length, and rotation requirements from frameworks such as NIST as well as include details and suggestions on factors to consider to help bolster your password security.
Joel Coakley is a Senior Offensive Security Consultant with Depth Security, a Konica Minolta Service. With an extensive background in consulting and network and Active Directory testing, Joel is focused on improving his methods on how to best communicate the risks small and enterprise organizations face alike with practical and tangible feedback tailored to each organization’s environment and business needs. Outside of work, Joel enjoys spending time with his wife, family and friends, spoiling his pets, and going on runs in preparation for a second marathon. If you’re interested in hiring Depth Security for Penetration Testing services, please visit our contact page, or email sales@depthsecurity.com.
